
I am happy to announce that Windows 11 24H2 finally supports that you can now directly disable UseRasCredentials in the Microsoft Intune Always On VPN Custom OMA-URI Settings profile.
Continue reading

I am happy to announce that Windows 11 24H2 finally supports that you can now directly disable UseRasCredentials in the Microsoft Intune Always On VPN Custom OMA-URI Settings profile.
Continue reading
On April 11, 2024, Microsoft has launched a public preview that allows the use of device-bound Passkeys for Microsoft 365 services / Microsoft Entra ID logins, which can be stored in the Microsoft Authenticator App. This development marks a significant step forward in the realm of secure authentication.
In this post, we’ll delve into Passkeys, understanding their benefits, prerequisites, and configuring them within Entra ID. Additionally, we’ll explore the user journey of generating and signing in with Passkeys.

Recently, Windows LAPS for Windows Server Active Directory was made available to the public, and I shared my initial test impressions:
Getting to Know Windows LAPS for Active Directory – First Look
As of April 21st, 2023, Windows LAPS for Azure Active Directory is now also accessible in a public preview. This presents an opportunity to test it in a cloud-only environment, and in this blog post, I will be sharing my initial testing impressions of Windows LAPS with Azure Active Directory in this scenario.
Continue reading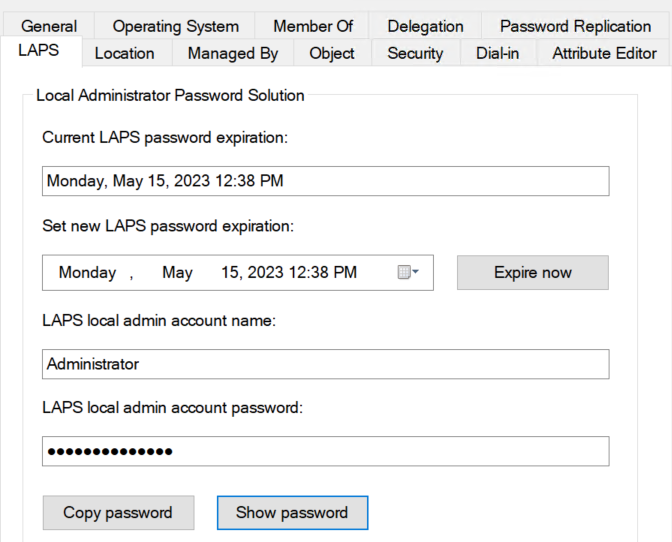
In October 2022, I published a blog post titled The 10 most important details about the upcoming Windows LAPS solution, which revealed that Microsoft was developing a new LAPS solution called Windows LAPS. This solution would address the long-awaited support for cloud-only devices. As of April 11, 2023, Windows LAPS for Windows Server Active Directory is now publicly available. Previously, Windows LAPS was only accessible through private preview. Unfortunately, Windows LAPS for Azure Active Directory remains in private preview and is not open to new customers. However, the Azure Active Directory LAPS scenario is anticipated to enter public preview in Q2 2023. In this blog post, I will be sharing my initial testing impressions of Windows LAPS with the Windows Server Active Directory (on-premises) scenario.

Endpoint Privilege Management (EPM) is one of the most anticipated features of the Microsoft Intune premium add-on suite and was already announced at Microsoft Ignite 2022. With EPM, Microsoft has finally developed a solution for assigning temporary administrator rights. Users no longer need to be made local administrators. Instead, your users can be given standard account permissions and be designated administrators for specific tasks. Microsoft has now released a first public preview. This blog article covers first test impressions about the new Microsoft Intune Endpoint Privilege Management feature.

This blog article covers the new Windows 11 22H2 security feature Enhanced Phishing Protection in Microsoft Defender SmartScreen and gives first impressions.

This blog article shows how to master the security recommendations of Microsoft Defender for Endpoint (MDE) with Microsoft Intune and achieve a device secure score above 95%.

This blog article covers the new Windows 11 22H2 security feature Smart App Control (SAC) and gives first impressions as well as recommendations.
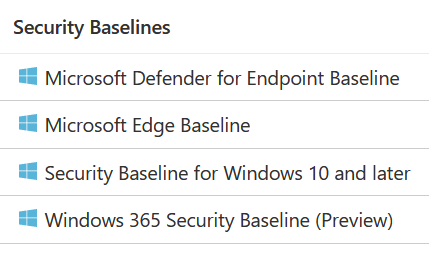
This blog article covers the implementation options of the different Microsoft Intune security baselines and gives an overview of policies that can impact your users.