
I am happy to announce that Windows 11 24H2 finally supports that you can now directly disable UseRasCredentials in the Microsoft Intune Always On VPN Custom OMA-URI Settings profile.
Continue reading

I am happy to announce that Windows 11 24H2 finally supports that you can now directly disable UseRasCredentials in the Microsoft Intune Always On VPN Custom OMA-URI Settings profile.
Continue reading
Endpoint Privilege Management (EPM) is one of the most anticipated features of the Microsoft Intune premium add-on suite and was already announced at Microsoft Ignite 2022. With EPM, Microsoft has finally developed a solution for assigning temporary administrator rights. Users no longer need to be made local administrators. Instead, your users can be given standard account permissions and be designated administrators for specific tasks. Microsoft has now released a first public preview. This blog article covers first test impressions about the new Microsoft Intune Endpoint Privilege Management feature.

While AppLocker has been around since Windows 7 and Windows Server 2008 R2, I have rarely found the solution in enterprises. The main reason was always that the implementation is very time and resource consuming and that you must constantly maintain a whitelist. This is a bummer, because the security gain is enormous when a solution like AppLocker is used. If you deal with the AppLocker rules intensively and have developed a good concept at the beginning, you will realize that you do not have to adjust the rule regularly and that the operation is not as complex as you thought.
This blog article shows the important things to consider when implementing AppLocker, how to create a usable basic ruleset that requires minimal maintenance, and how to manage with Microsoft Intune.

This blog article covers the new Windows 11 22H2 security feature Enhanced Phishing Protection in Microsoft Defender SmartScreen and gives first impressions.

Microsoft Ignite 2022 took place from October 12-14, happily as a hybrid event, online and onsite in Seattle. Under the headline “Do more with less with the Microsoft Cloud“, Microsoft presented over 100 new solutions or updates to existing products. This blog article presents my top 10 takeaways from Microsoft Ignite 2022 with a focus on Modern Workplace, Microsoft 365 and Security. In conclusion, I will honor my favorite session and give my overall impression of Microsoft Ignite 2022.

This blog article shows how to master the security recommendations of Microsoft Defender for Endpoint (MDE) with Microsoft Intune and achieve a device secure score above 95%.

This blog article covers how to deploy Windows Features like Windows Sandbox or Hyper-V with Microsoft Intune.
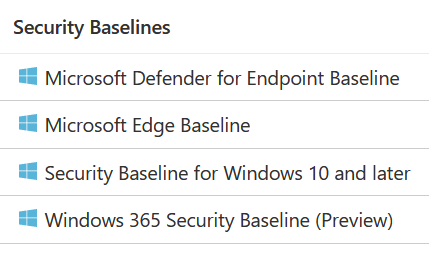
This blog article covers the implementation options of the different Microsoft Intune security baselines and gives an overview of policies that can impact your users.